Using Jenkins to Monitor SSL Certificates
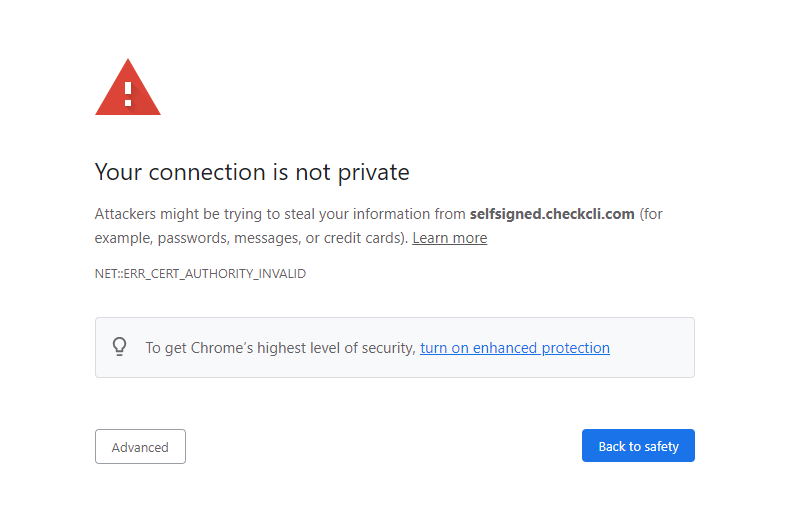
There are great tools like Let’s Encrypt to generate free HTTPS certificates for your websites, but sometimes certbot renewals fail. Everyone should have some level of monitoring to ensure that your site has a valid SSL. It’s always embarrassing to go to a site you run and find the dreaded blocked page.
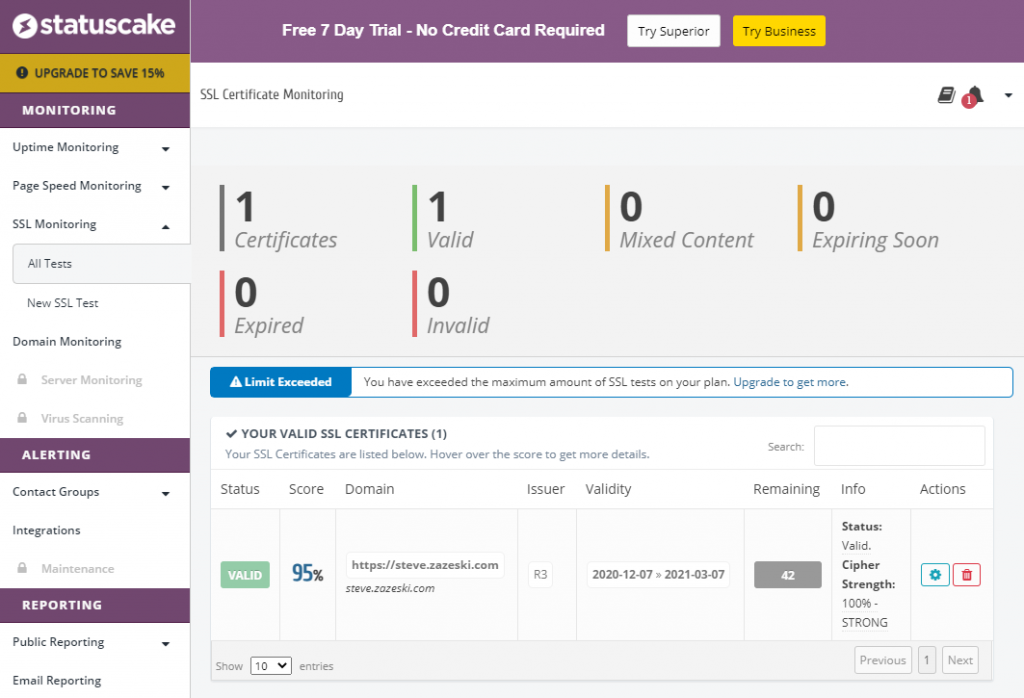
Option 1 : Statuscake
If you are looking for a no-hassle hosted solution, Statuscake is set up to monitor server uptime and SSL certificates of public servers. The free version limits you to a single SSL certificate check and the next tier lets you check 50 domains for $25/month. It has built-in email or slack notifications.
However, if you have a Jenkins instance and want to check as many domains as you like or want to check servers that are not public (behind a firewall), then you have two options:
Option 2 : Jenkins Job using curl
A very simple way to check a site’s certificate is to call curl. Most Linux systems have curl already loaded, and it will return an exit code of 0 if everything is ok.
In the Jenkins job, add a build step with Execute Script
curl https://expired.badssl.com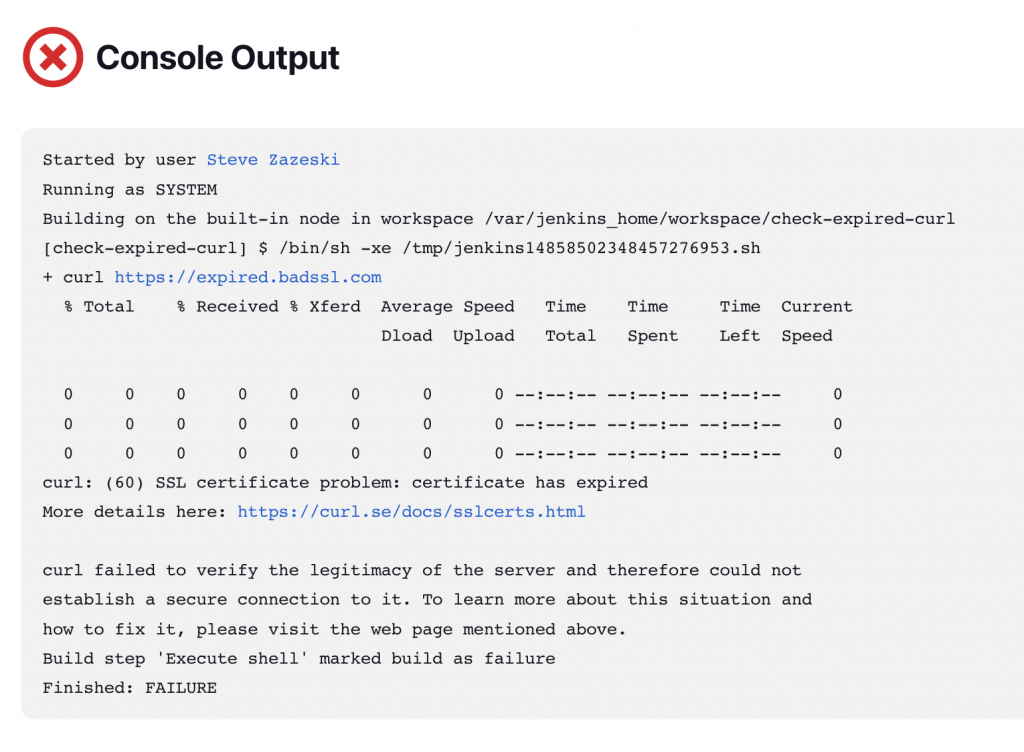
However, when things go wrong, curl is not very helpful to point you to the issue.
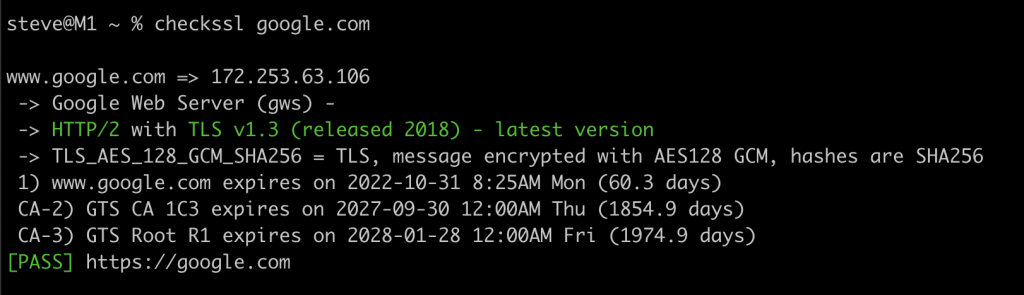
Option 3 : Jenkins Job using checkssl
However, if you are looking for a more detailed SSL check that returns a better report of why the SSL check failed, look at the CLI tool checkssl.
checkssl -days=5 expired.badssl.com google.com reddit.com
Creating the Jenkins Job
- Create a New Item
- Enter a task name (ideally use a name without spaces like check-website)
- Select Freestyle project
- Click Ok
- Enter a Description if desired
- Check Discard old builds and set Max # of builds to keep to 7
- Check Build periodically and set it to
@daily - Click Add a build step with Execute Shell
stat checkssl > /dev/null || wget -O checkssl https://get.checkcli.com/checkssl/linux/64 && chmod +x checkssl
./checkssl -days=7 steve.zazeski.com checkssl.orgTest URLs
If you want to test out what happens with the various monitoring solutions above, just try them with one of these:
- https://www.checkcli.com – should pass
- https://expired.badssl.com – should fail
- https://self-signed.badssl.com – should fail
- https://wrong.host.badssl.com – should fail

If the ssl certificate expires, the jenkins job fails. Is it possible for the jenkins job to be successful even if the ssl certificate expires
Yeah, if you want the job to always pass, on the ./checkssl line in the jenkins job if you add at the end a || true it will always pass.